Tennessee passed its own data privacy law in May 2023. It went into effect on July 1, 2025. And if you run a business in this state, you should probably know what it says.
The Tennessee Information Protection Act, or TIPA, gives Tennessee residents new rights over their personal data and puts specific obligations on the businesses that collect it. It sits alongside similar laws in California, Virginia, Colorado, and a growing list of other states. But TIPA has a few quirks that make it worth paying attention to on its own.
Here’s what TIPA actually requires, who it covers, and what you should do about it.
Who TIPA actually applies to
Before you panic, take a breath. TIPA has some of the highest applicability thresholds of any state privacy law in the country.
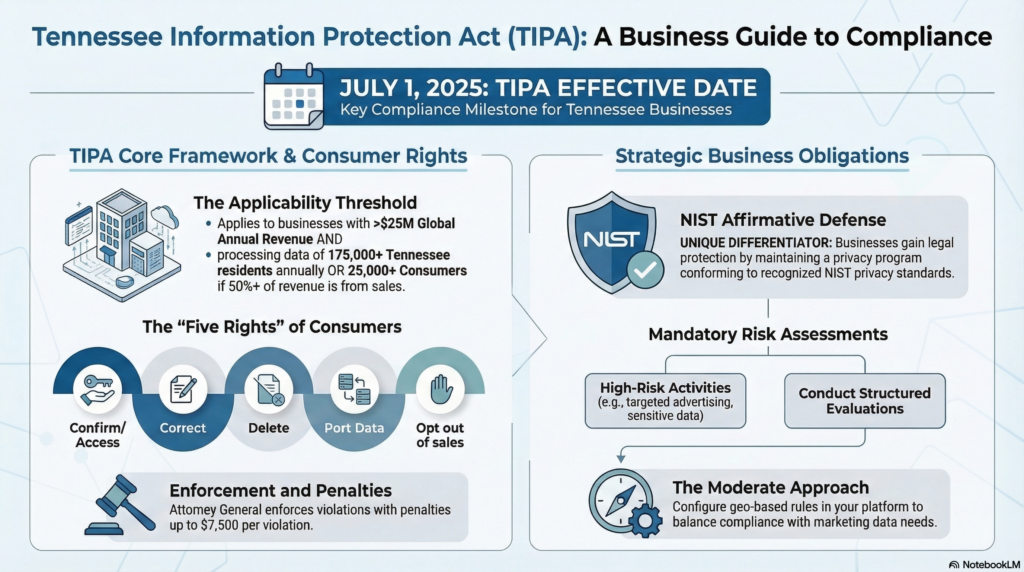
To fall under TIPA, your business needs to meet ALL of the following:
You must generate at least $25 million in annual revenue. On top of that revenue threshold, you also need to hit one of two data volume triggers. Either you process personal information on 175,000 or more Tennessee consumers in a calendar year, or you process data on at least 25,000 Tennessee consumers while getting more than half your revenue from selling that data.
That 175,000 consumer threshold is the highest of any state. California, Virginia, and Colorado all set theirs at 100,000. So TIPA catches fewer businesses by design.
Several types of organizations are explicitly exempt. Government agencies, nonprofits, higher education institutions, and entities already covered by HIPAA or the Gramm-Leach-Bliley Act don’t need to worry about TIPA compliance specifically. Tennessee also became the first state to explicitly exempt state-licensed insurance companies from its privacy law.
Why smaller businesses should still care
Here’s the thing. Even if your company doesn’t hit those thresholds, TIPA still matters to you. There are two reasons.
Your larger clients might require it. If you provide IT services, consulting, or any kind of data processing for a company that IS subject to TIPA, they’re legally required to have data processing agreements with you. Those agreements will spell out security requirements, confidentiality obligations, and how you handle their customers’ data. You may not be directly regulated, but your contracts will start reflecting TIPA’s requirements.
It sets a baseline for what “reasonable” looks like. When a Tennessee court or regulator evaluates whether a business took reasonable steps to protect data, they’re going to look at what the law says. TIPA creates a clear benchmark. If a data breach hits your company and you haven’t taken basic precautions, the existence of TIPA makes it harder to argue you didn’t know what was expected.
What rights do Tennessee consumers get?
TIPA grants five rights to Tennessee residents when they’re acting in an individual or household context (not as employees or in a B2B capacity).
People can ask whether you’re processing their data, and get a copy of it. They can also request corrections to inaccurate information, ask you to delete their data, or get it in a portable format they can take to another service.
The big one for most businesses is the opt-out right. Consumers can tell you to stop selling their data, stop using it for targeted advertising, and stop profiling them in ways that produce legal or similarly significant effects. If your business model touches any of those activities, this is the right that will generate the most requests.
You have 45 days to respond when someone exercises any of these rights. You can extend that by another 45 days if you need to, but you have to tell them why.
What businesses are required to do
The obligations under TIPA fall into a few categories. None of this should be shocking if you’ve followed privacy law developments over the past few years, but it’s worth spelling out.
Publish a clear privacy notice. Your privacy policy needs to disclose what categories of data you collect, why you collect it, who you share it with, and how consumers can exercise their rights. This isn’t optional. It needs to be accessible and written in plain language.
Practice data minimization. You can only collect data that’s adequate, relevant, and reasonably necessary for the purposes you’ve disclosed. Collecting everything “just in case” doesn’t fly under TIPA.
Get opt-in consent for sensitive data. While most of TIPA operates on an opt-out basis (collect first, let people opt out later), sensitive data flips that model. If you’re processing information about someone’s health, race, religion, sexual orientation, biometrics, precise geolocation, or immigration status, you need their explicit consent first. Children’s data under 13 also requires opt-in.
Conduct data protection assessments. Before you engage in targeted advertising, sell personal data, process sensitive information, or do profiling, you need to document a formal risk assessment. These aren’t just paperwork. They force you to think through the actual risks and whether the benefits justify them.
Lock down your vendor contracts. If you use processors (any third party that handles personal data on your behalf), TIPA requires a binding contract that defines roles, data handling requirements, confidentiality, and security obligations. Handshake agreements won’t cut it anymore.
Maintain reasonable security safeguards. TIPA requires administrative, technical, and physical security measures appropriate to the sensitivity of the data you handle. What counts as “reasonable” scales with your business size and the type of data involved.
Penalties and enforcement
TIPA is enforced exclusively by the Tennessee Attorney General. There’s no private right of action, so individual consumers can’t sue your business for TIPA violations. California allows limited consumer lawsuits over data breaches. Tennessee doesn’t.
If the AG does come knocking, you get a 60-day cure period to fix the problem before any penalties kick in. This cure period is permanent. It doesn’t expire or sunset like the ones in some other states.
Penalties go up to $7,500 per violation. Knowing or willful violations can trigger treble damages, which means those penalties triple. The AG can also seek injunctions, attorney fees, and investigative costs.
The NIST safe harbor, and why it matters
This is the part of TIPA that privacy lawyers keep talking about, and with good reason.
Tennessee is the first state to include a statutory affirmative defense tied to the NIST Privacy Framework. In plain English, if your business maintains a written privacy program that reasonably conforms to the NIST Privacy Framework (or a comparable documented standard), you can use that as a legal defense against enforcement actions.
Why does this matter? Because most privacy laws leave “reasonable practices” undefined. You’re left guessing. TIPA lets you point to a specific framework and say “we follow this.” And the NIST Privacy Framework is free. You can download it from nist.gov and start implementing it today.
The catch is that your program needs to be updated at least every two years to maintain the defense. A privacy program you wrote in 2025 and never touched again won’t protect you in 2028.
How TIPA compares to other state privacy laws
If you operate in multiple states, you need to understand where TIPA sits relative to its peers.
It’s more business-friendly than California. TIPA doesn’t require you to recognize universal opt-out signals like Global Privacy Control. California does. TIPA has a permanent 60-day cure period. California’s expired. TIPA has no private right of action. California allows limited consumer lawsuits.
It’s closest to Virginia and Utah. The structure and enforcement approach are very similar. If you’re already compliant with Virginia’s CDPA, you’re most of the way to TIPA compliance.
The thresholds are higher than almost everywhere else. At 175,000 consumers, Tennessee requires a larger data footprint than any other state before the law kicks in. Texas and Nebraska don’t even have a revenue threshold, which means much smaller businesses can be covered in those states.
Practical steps you should take right now
Whether TIPA directly applies to your business or not, these steps put you in a better position as more states pass similar laws.
Start with a data inventory. Map out what personal data you collect, where it lives, how it flows through your systems, and who has access. You can’t protect what you don’t know about. Most businesses we work with are surprised by how many systems store customer data once they actually look.
Then update your privacy policy. Make sure it reflects your current practices, not what you were doing three years ago. If your privacy policy is a copy-pasted template from 2019, it’s time for a rewrite. Disclose the categories of data you collect, your purposes, third-party sharing, and how consumers can exercise their rights.
Build a consumer request workflow. If someone emails tomorrow asking for their data or requesting deletion, do you have a process for that? You need one. Who receives the request? How do you verify their identity? Where does data live across your systems? How do you track the 45-day clock?
Review your vendor contracts. Every third party that touches personal data on your behalf needs a data processing agreement. Your cloud providers, your CRM, your email marketing platform, your IT service provider. If any of those relationships are running on a handshake, that’s a gap.
Consider aligning with the NIST Privacy Framework. Even if TIPA doesn’t directly cover you, a documented privacy program gives you something concrete to point to if questions come up. And if a future law does cover you, you won’t be starting from scratch.
Your IT provider can help with the technical side of all this. Access controls, encryption, data backup, incident response procedures. If you’re in healthcare or legal services, you probably have some of these in place already through HIPAA or industry requirements, but TIPA may require additional documentation. If you’re in healthcare specifically, see our HIPAA IT requirements guide for 2026 for the ten controls OCR is currently enforcing.
Where this leaves Tennessee businesses
TIPA’s thresholds are high and its cure period is generous. Most small businesses won’t be directly regulated by it. But it’s been the law since July 2025, and the AG has enforcement power with penalties up to $7,500 per violation (tripled for willful violations).
The smart move is to get your data practices documented now, while nobody’s knocking on your door, rather than scrambling after a breach or a vendor audit. The NIST safe harbor alone makes this worth doing. It’s a free framework that doubles as a legal defense.
If you’re not sure where your business stands, get in touch or take our free IT health check to find the gaps before someone else does.