Most small business owners hear “ransomware” and picture a number. Maybe it’s the number a TV news anchor said last week. Maybe it’s the number a vendor used to scare them in a sales meeting. Either way, it’s almost always wrong.
The ransom is never the real cost. Not even close.
Here’s what a ransomware attack actually costs a 20-person company in 2025 and 2026, with the math broken down line by line. If you run a business in Franklin, Nashville, or anywhere in Tennessee, this is the post your insurance agent should have already sent you.
The ransom is the cheapest part
Coveware’s Q4 2025 report put the median ransom payment at $325,000. That number includes larger companies, so it skews high for anyone with under 50 employees. Sophos found that businesses with under $250 million in revenue face median demands under $350,000. For a small operation, the initial demand often lands between $5,000 and $10,000, which sounds almost affordable.
That’s the trap. Attackers price the first demand to feel payable. They want you to wire it fast. The actual cost of the incident has nothing to do with that number.
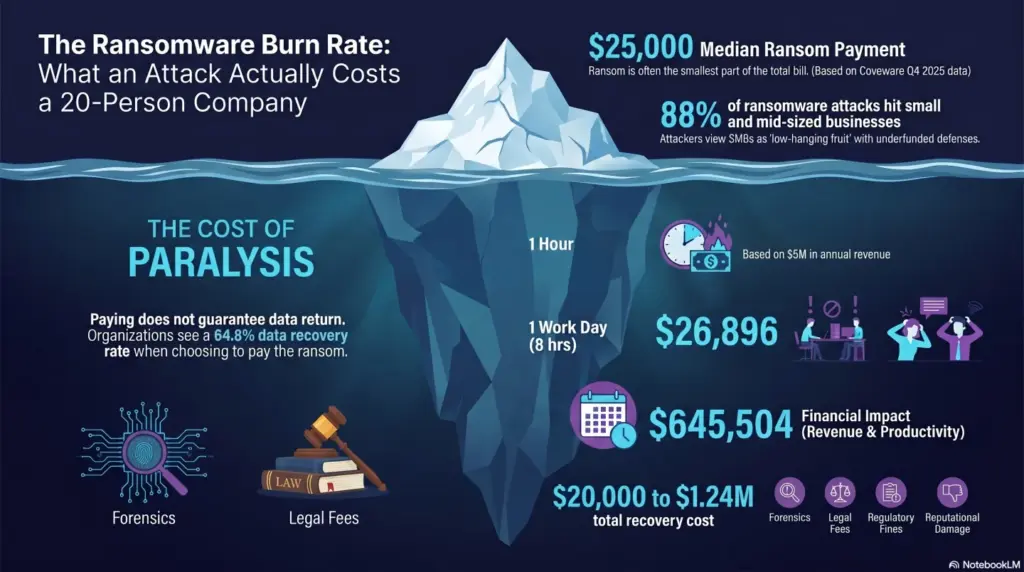
Entre’s SMB report puts total ransomware recovery costs between $120,000 and $1.24 million. Sophos pegs the global average recovery cost at $1.53 million, excluding the ransom itself. For a 20-person company, realistic total damage lands somewhere between $200,000 and $800,000 once everything is tallied.
Let’s tally it.
Where the money actually goes
Here’s a realistic breakdown for a 20-person professional services firm doing $5 million in annual revenue, hit with a standard double-extortion attack.
Downtime. E-N Computers modeled exactly this scenario. A 20-person company at $5M revenue loses $3,362 every hour it’s down. That’s $4,808 in hourly revenue plus $1,797 in hourly lost productivity. The average ransomware disruption lasts 24 days per Statista. Even if only a third of those are standard 8-hour workdays with full impact, that’s over $215,000 in pure downtime cost.
Recovery labor. Emergency incident response runs $300 to $500 per hour. A typical SMB engagement burns 80 to 200 hours across forensics, eradication, and rebuild. Call it $40,000 on the low end.
Legal and notification. If any client data was exfiltrated, and Coveware says 87% of 2025 attacks now involve data exfiltration, you owe notifications. Tennessee’s data breach notification law triggers when personally identifiable information is compromised. Legal review, state AG filings, and notification letters typically run $15,000 to $50,000 for an SMB.
Cyber insurance deductible. If you have a policy, the deductible for SMBs averages $25,000 to $100,000. Cybereason found that 42% of insured companies reported their policy covered only a small fraction of total damages.
Lost business. Clients who find out you were breached sometimes leave. Prospects who were about to sign sometimes don’t. This one is hard to measure, but for a 20-person professional services firm it’s almost never zero.
Ransom, if paid. If you pay, the small-business demand typically falls between $20,000 and $200,000. 37% of victims paid in Q4 2025 per Coveware, which is a record low.
Add it up. For a 20-person company, a ransomware attack costs $300,000 to $700,000 before anyone pays the ransom. The ransom is maybe 10 to 30% of the total.
Paying the ransom doesn’t actually fix it
This is the part nobody wants to hear. The HHS reports that organizations who pay the ransom get back 64.8% of their data on average. Cybereason found that 46% of paying victims regained access, but most of the restored data was corrupted.
Then there’s the sequel. Between 69% and 80% of businesses that pay a ransom get attacked a second time, according to Cybereason and Entre. The attacker either comes back, sells your access to another group, or lets a partner take a second swing. Your credentials are already compromised. Your network map is already sold. You paid once, so you’ll probably pay again.
Paying is a tax. It buys a 65% chance of getting your files back and a 70% chance of being attacked again within a year. That’s a bad trade.
How the attack actually unfolds
For a 20-person company, the attack almost always starts one of two ways. Sophos data shows 30% begin with compromised credentials, usually a password phished or bought on a dark web market. Another 29% start with an unpatched software vulnerability. Phishing emails cause between 18% and 35% of all breaches.
Here’s what the timeline looks like.
Day one, an employee clicks a link in an email that looks like it came from a vendor. They enter their Microsoft 365 password. The attacker now has access. Nobody notices.
Days two through five, the attacker logs in quietly during off-hours. They map the network. They find the file server, the backup location, the accounting system. Entre and Barracuda report the median dwell time from initial access to ransomware execution is five days.
Day six, during a weekend or overnight, the attacker runs the encryption. Sophos found 50% of 2025 attacks resulted in data encryption. Before encrypting, they usually copy everything off-site first. 87% of attacks in 2025 involved data exfiltration, which gives the attacker a second lever: pay us or we publish your client list.
Monday morning, your team shows up to blank file servers, a ransom note on every screen, and a Bitcoin wallet address. Your 24 days of downtime just started.
What actually prevents it
Every MSP has a list of controls to sell you. Here are the ones that actually matter, ranked by effect on SMBs based on Sophos data.
Real backups, tested monthly. 68% of ransomware victims use backups to restore, and 97% recover their data when backups are maintained correctly. The 3-2-1 rule still holds: three copies, two different media, one off-site and offline. The key word is offline. If your backup is reachable from your production network, the attacker encrypts it too. This is the single highest-leverage control you can put in place.
Multi-factor authentication on everything. MFA stops the 23 to 30% of attacks that start with stolen credentials. Every email account, every remote access tool, every admin login.
Patch management. 32% of attacks enter through software vulnerabilities that already had patches available. If you’re running a quarterly patch cycle, you’re probably two or three cycles behind the attackers.
Managed detection and response. Sophos found that proactive monitoring stopped 44% of ransomware attacks before encryption in 2025. MDR means somebody is actually watching the alerts at 2 AM when the attacker is active.
Employee training that isn’t a checkbox. Short monthly phishing simulations work. Annual compliance videos don’t.
Two small businesses who lived through it
Plainfield, an organization roughly the size of a 20-person company, got a $199,000 ransom demand. They refused. Comparitech reports the total cost to rebuild systems independently came to $350,000. They saved the ransom and spent 1.75x that amount on recovery instead.
A Virginia wrecking company with $1 million in annual revenue got hit with a $5,000 to $10,000 demand on their inventory and sales systems. E-N Computers reports the final recovery cost crossed the $120,000 baseline. The ransom would have been 5% of the total damage.
Both stories tell you the same thing. The ransom is the sticker price. The real cost is always in the recovery.
What this means if you run a 20-person business in Tennessee
Three questions to ask yourself this week.
First, if your entire network went dark tomorrow morning, how long would it take to restore from clean backups? If you don’t know, find out. If the answer is more than 48 hours, that’s a problem worth fixing before the attack, not after.
Second, does every account with admin access to anything require MFA? Not “we rolled it out last year.” Right now, today, every single account.
Third, who is watching your systems at 2 AM on a Saturday? If the answer is nobody, you’re relying on the attacker to make noise. They won’t.
Charger IT handles all three for businesses across Tennessee and neighboring states. If you want a second set of eyes on your current setup, we run free 30-minute reviews: no pitch, no pressure, just a look at where you are. Schedule an IT health check or get in touch and we’ll walk through it.
Ransomware is a math problem. The math favors the defender, but only if the defense is in place before the attacker arrives.